How hackers use idle scans in port scan attacks
Por um escritor misterioso
Descrição
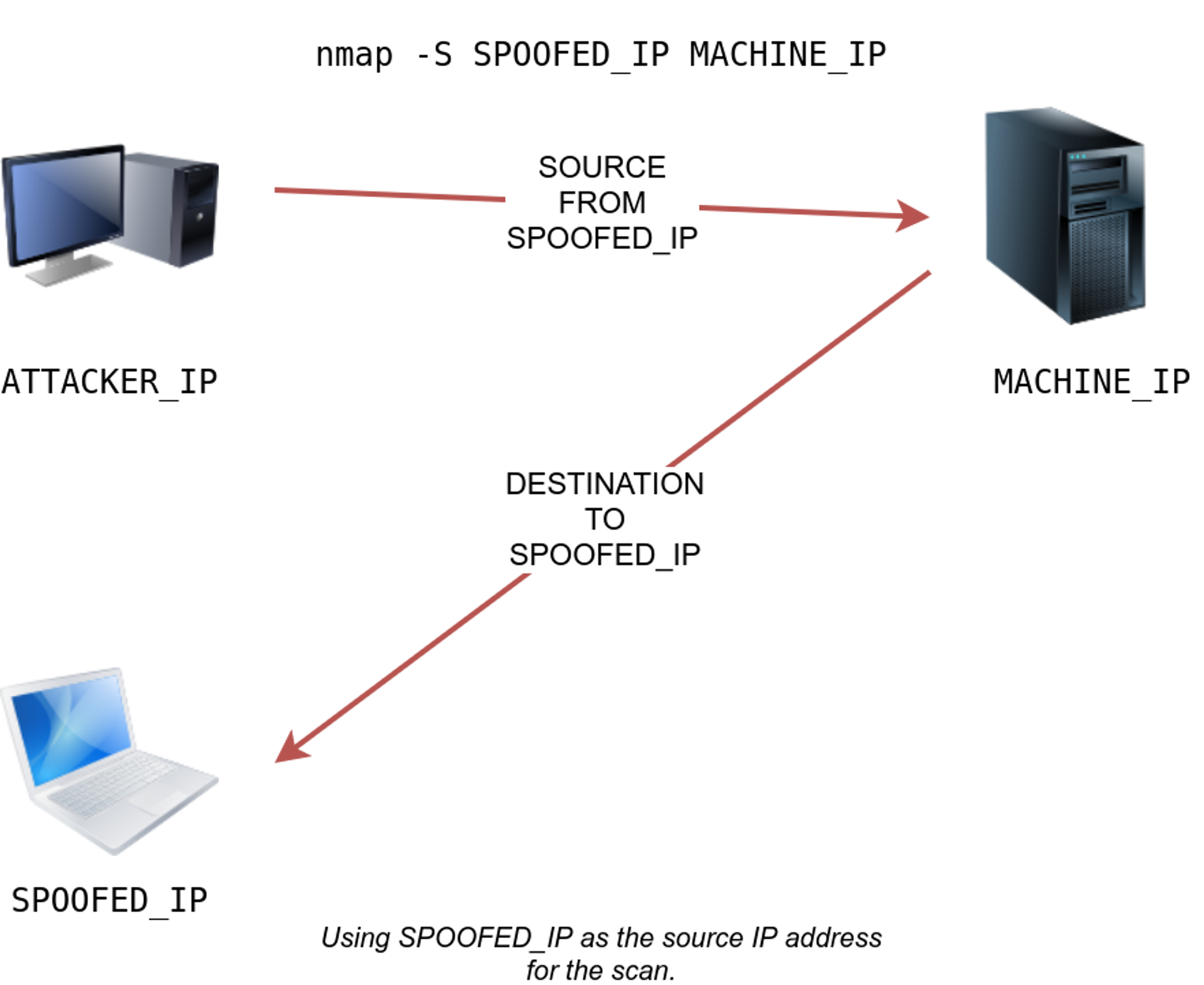
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.

Nmap – How to Use Nmap – Spyboy blog

What Is A Port Scan? How To Prevent Port Scan Attacks?

How to Do an Idle Scan with Nmap « Null Byte :: WonderHowTo
The Ultimate Guide to Port Scanning using Nmap
PPT - Port Scanning PowerPoint Presentation, free download - ID:4633948
What is a Cyber Attack? Definition and Related FAQs

How hackers use idle scans in port scan attacks

Port Scanning - an overview
What is a Cyber Attack? Definition and Related FAQs

Port Scanning: A Comprehensive Guide for Safeguarding Cyberspace
Scanning, Footprinting, Reconnaissance, and Scanning

Port Scan Attack】Definition, Examples, and Prevention

Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan
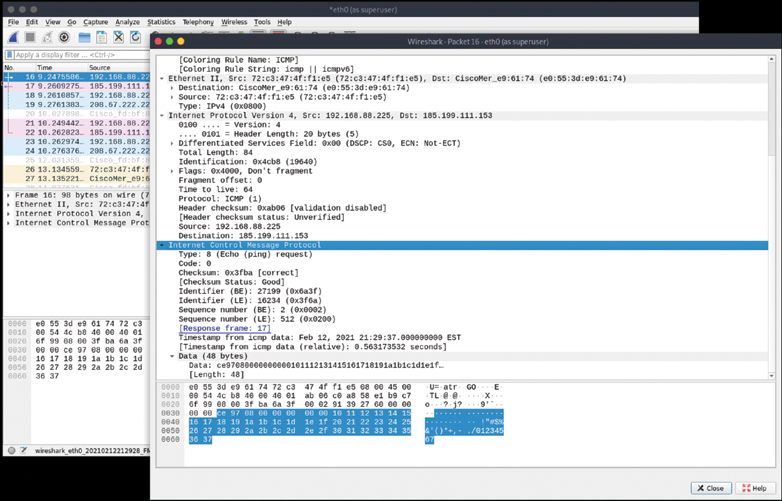
PDF) Surveying Port Scans and Their Detection Methodologies

Port Scanning - an overview
de
por adulto (o preço varia de acordo com o tamanho do grupo)