Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
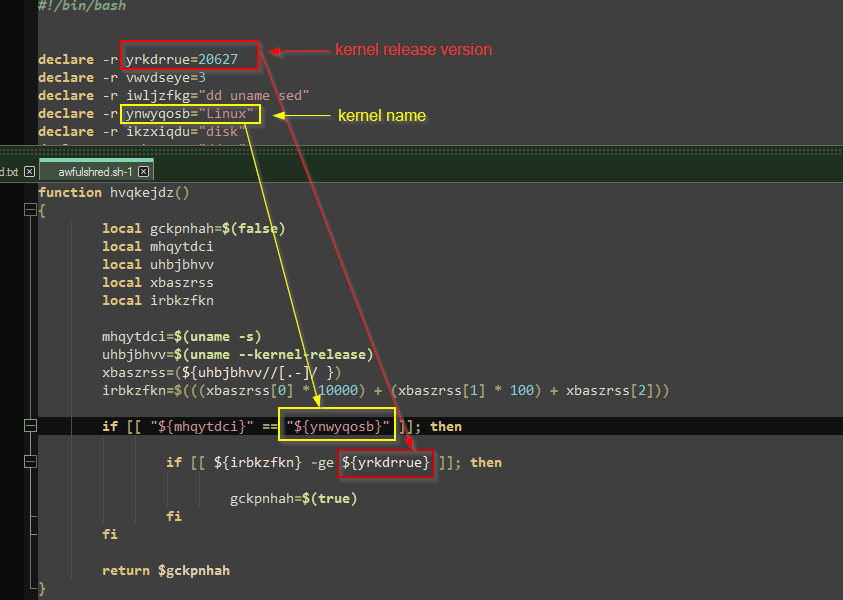
Threat Update: AwfulShred Script Wiper
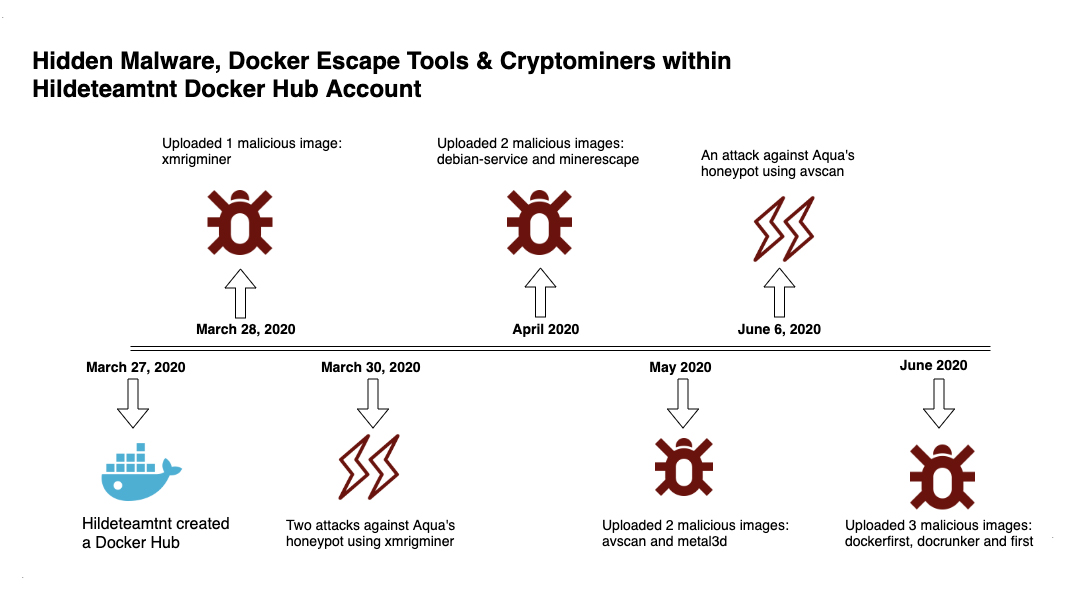
Deep Analysis of TeamTNT Techniques Using Container Images to Attack

Six Ways Malicious Linux Shell Scripts Evade Defenses

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
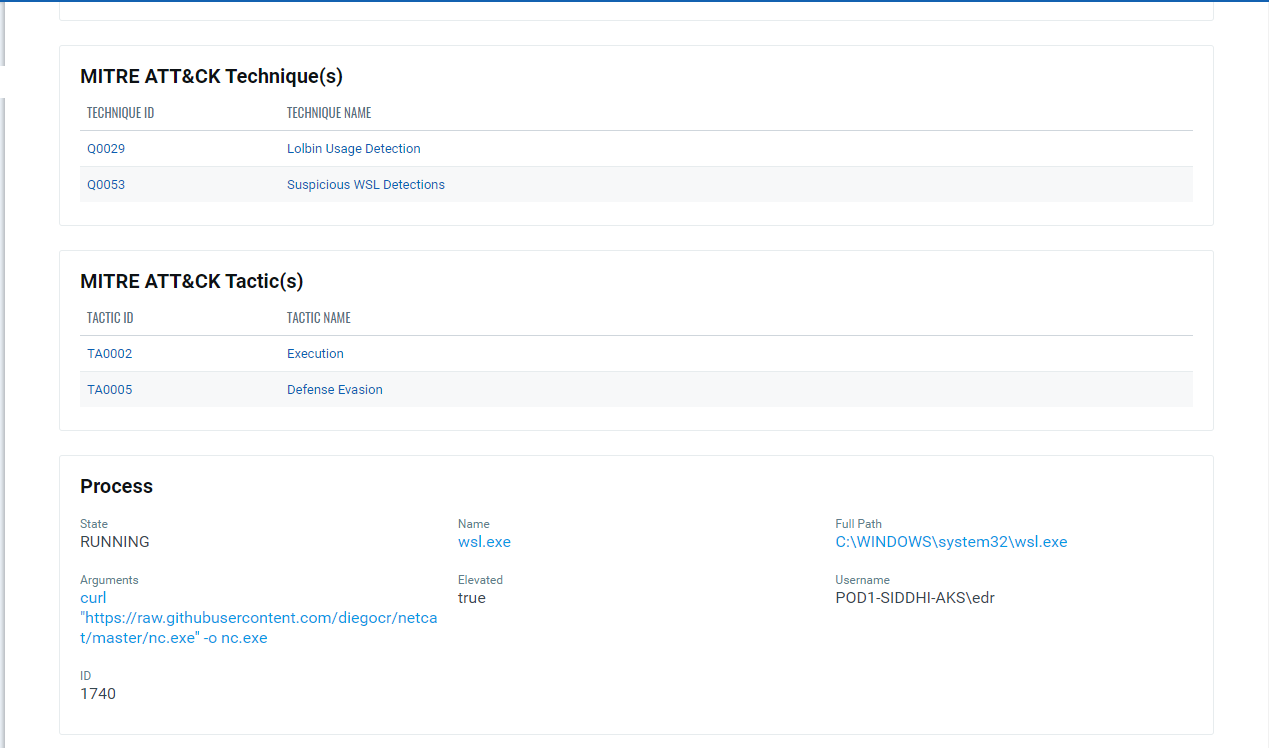
Implications of Windows Subsystem for Linux for Adversaries
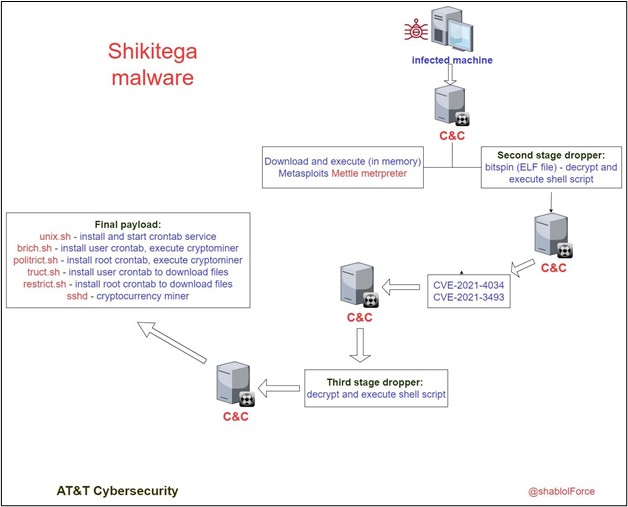
Shikitega - New stealthy malware targeting Linux

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
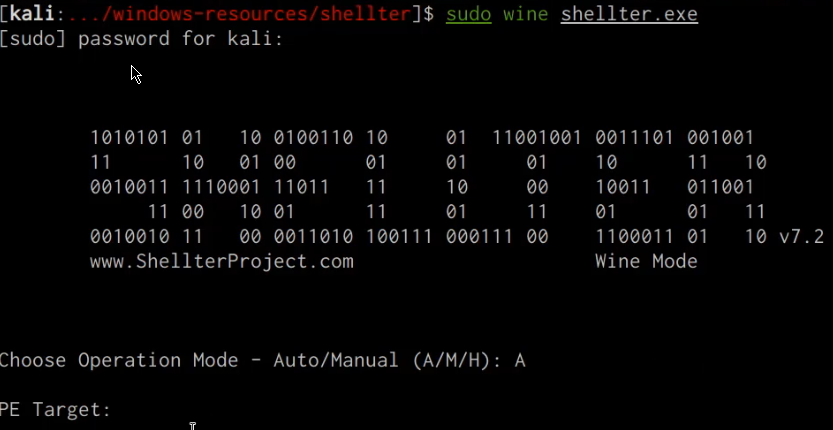
Windows Red Team Defense Evasion Techniques - HackerSploit Blog

Windows Red Team Defense Evasion Techniques - HackerSploit Blog
de
por adulto (o preço varia de acordo com o tamanho do grupo)